Eagle Point-of-Sale System Security
September 19, 2023

At DilSe.IT, we take pride in creating innovative processes and technologies that add value for Ace Hardware store owners, managers, and associates.
Building on last month’s Desk of Andy blog post where we talked about unsecured computers, I thought a good follow-up would be to talk about properly securing your Epicor Eagle point-of-sale and inventory management system.
One of the most important things to be aware-of for your Eagle system security is Payment Card Industry (PCI) compliance which refers to a set of security standards and guidelines designed to ensure the secure handling, processing, and storage of credit card information. The PCI Data Security Standard (PCI DSS) is the framework which outlines these guidelines for retailers. Compliance involves a wholistic approach:
- Building and maintaining a secure computer network
- Protecting cardholder data
- Maintaining a vulnerability management plan
- Implementing strong access control measures
- Regularly monitoring and testing your network, and
- Maintaining an information security policy
I will focus this email what you need to do to protect cardholder and other confidential data in your Eagle system.

Epicor has implemented 3DES encryption and strong transactional security within Eagle. If you are running Eagle from the cloud, you have this turned-on automatically. If you are running an on-premises server, you should ensure that you also have it turned-on. This option encrypts all credit card information stored within Eagle making it much more difficult to steal.
Several Eagle option settings control whether your Eagle system is ready for PCI compliance: You should confirm that Option 1098 “SecureAccess enabled” is set to yes. Option 1099 “CHILKAT on System” is set to yes (CHILKAT is a 3rd party API platform). Option 8888 “Eagle N Series on System” is set to yes. And, Option 1061 “PADSS Compliant System” is set to yes (PADSS is an encryption protocol).
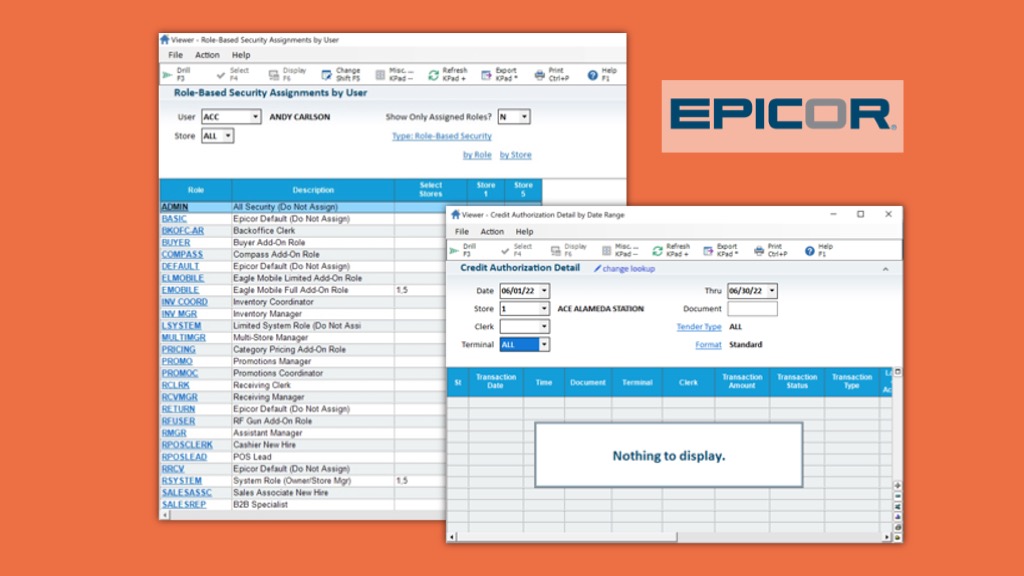
Per both PCI DSS and Ace Way of Retailing (AWOR) guidelines, you must use Role-Based Security (Option 550) on your Eagle system. Terminal-Based Security will not meet compliancy requirements. You must also enable High-Security Passwords on your Eagle system using Option 150. You can set the password expiration window using Option 1333 – this must be 90 days or less. You can also control other behaviors relating to passwords using Options 1330 through 1332.
Any employee with access to credit card data should have a High-Security Password. In particular, Security Bit 689 “View full customer credit card number” and Security Bit 691 “View full customer credit card number (decrypted mode)” should be assigned only if absolutely necessary for the employee’s job function. A good practice is that any employee with access “Cash Drawer Balancing (CDB),” the “Display Cash Drawer (DCD),” or “Credit Card Authorization Detail (CARD)” viewers should have a High-Security Password.
You should also carefully consider how your Roles are built and maintained. I find it useful to define several functional Roles:
- SYSTEM – Owner exclusive (High-Security)
- MULTIMGR – Multi-store manager or GM (High-Security)
- BKOFC – Back office coordinator or clerk (High-Security)
- MGR – Assistant manager and above (High-Security)
- SUPV – Shift supervisor or store key-holder (High-Security)
- POSLEAD – Shift lead or cashier lead (High-Security)
- POSCLERK – Cashier
- SALESASSC – Sales associate (not trained on cashier)
And then, create several “add-on Roles” you can assign for specific features in-addition to the Roles above:
- BUYER – Access to purchase orders
- COMPASS – Access to Compass business intelligence
- EMOBILE – Access to use Eagle Mobile (Eagle Mobile+ is handled with a separate license manager)
- PRICING – Access to Category Pricing
- PROMO – Access to MIP, MDP, and the ability to change QOH in IMU which is required to set up coupons
- RFGUN – Access to Telnet CE on the Motorola RF gun
This Role design allows you to add security permissions as an employee is trained or promoted to positions with higher authority.
Eagle users should never share logins and passwords. I have seen this commonly happen when using Zebra devices or RF guns, but this is unsafe from a cyber security perspective. Once an employee is trained to use these mobile devices, they should be assigned the appropriate security Role on their personal Eagle login.
Automatic sign-off from Eagle should be enforced at 30 seconds to 1 minute at point-of-sale, 5 minutes for other sales floor computers, and 15 to 30 minutes for computers secured in an office area. Windows screen saver time-outs and passwords should also be implemented as described in last month’s blog post.
Epicor Eagle is a powerful computer system capable of running your Ace Hardware store and keeping customer data safe if properly implemented and maintained. Your Role-Based Security profiles and Option settings will determine if your Eagle software is ready for you to maintain PCI compliance. DilSe.IT assists many Ace Hardware clients with attaining and maintaining PCI Compliance and cyber security best practices. For more information, please email us at DeskOfAndy@DilSe.it